What happens to your protocol if the RPC provider you depend on goes dark?
What if the node that you depend on for your transaction data is shared with dozens of other dApps, all fighting for the same bandwidth during a market surge?
The questions are ones that Web3 builders who are choosing Solana cannot afford to ignore. They are the difference between success and an outage that costs real money.
Counterparty exposure within Solana RPC infrastructure is perhaps the most underestimated risk within the Web3 ecosystem. It has nothing to do with smart contract exploits or on-chain attacks. It is the unspoken dependencies you have on third-party infrastructure, such as shared endpoints, centralized API access, and infrastructure arrangements that can throttle you at the worst possible time.
As Solana continues to grow and reach new heights, with over 400 million transactions processed on peak days, the importance of getting your infrastructure game on point has never been higher. The best Solana RPC provider is not the one that has the fastest nodes; it is the provider that exposes you to the least amount of operational risk between your application and the blockchain.
Why Counterparty Exposure Matters More Than Ever in Solana

While networks with slower block times and larger latency windows can accommodate mistakes, Solana necessitates connections that are rock-solid in terms of latency.
If your Solana RPC is lagging behind, failing requests, or limiting connections during the middle of your session, it is certainly going to cause noticeable effects that are not recoverable. This includes failed transactions, outdated information, or an overall subpar user experience that makes your users seek an alternative elsewhere.
The edge of counterparty exposure, the risk that the third party you’re relying on will not perform, takes on an extra level of sharpness in this environment. The more you’re dependent on other infrastructure, particularly shared infrastructure, the higher the exposure.
The Numbers Paint a Clear Picture
- Solana handles 2,000 to 4,000 transactions in one second. The tolerance of latency is extremely low in Solana’s ecosystem.
- In fact, in 2023 alone, there were several outage incidents involving major public Solana RPC endpoints, with some of these outages lasting several hours during high-traffic periods.
- A majority of DeFi protocol failures which are not related to smart contact vulnerability trace back to infrastructure dependencies, not on-chain logic.
- Teams using shared Solana RPC API access frequently report rate limiting during peak demand, precisely the moment when reliable access is most critical.
Why Solana Is Particularly Sensitive
- High throughput means high dependency. More transactions processed means more RPC calls per second.
- Validator updates and network upgrades can shift RPC behavior rapidly, requiring infrastructure partners to stay current.
- The architecture of Solana’s fee markets is such that any level of delay in the RPC endpoint will impact the success of the transactions and the priority of the transactions.
- dApps, wallets, DEX aggregators, and MEV bots are all competing for the endpoint bandwidth.
Stop sharing your Solana RPC bandwidth with bots and competitors. Take control today.
Where Counterparty Exposure Typically Emerges in RPC Setups
Understanding where the exposure resides is the first step to reducing it. The majority of Web3 builders have accumulated counterparty risk quietly, often unaware of how dependent their product has become on these agreements that were not built for production-grade reliability.
The Public Endpoint Problem
- Public Solana RPC endpoints, although useful for testing, are subject to an indeterminate number of users. There is no SLA, priority, or consequence if they slow down or stop working.
- Free public endpoints have rate limits as few as 100 per 10 seconds, which even a small dApp can exceed in a matter of minutes.
- Anyone using a public Solana RPC API for production workloads is effectively accepting unlimited counterparty exposure with zero contractual recourse.
- Public nodes may not sync well after upgrade, and this will cause your application to read from outdated state.
Third-Party API Aggregators
- Many teams route Solana RPC API calls through aggregators that manage multiple upstream node providers. This adds a layer of abstraction and a layer of risk.
- If the aggregator’s routing logic fails, your requests may hit degraded nodes without your knowledge.
- Aggregator pricing models can introduce unpredictable cost exposure during high-volume periods, aligning financial risk with operational risk.
- Vendor concentration risk increases if your aggregator sources node capacity from a small set of upstream providers.
Absence of Node Clusters
- A single server for Solana RPC is a single point of failure.
- Scheduled maintenance, DDo attacks, or cloud outages in some regions can cause the single server solution to become unavailable without an alternative.
- Teams with a single Solana RPC node relationship often discover the gap in their setup during an incident, not before.
- Contract structures with a single provider often lack the flexibility to scale capacity rapidly during traffic surges.
The Risks of Relying on Shared or Public Solana RPC Endpoints
If you are still relying on shared Solana RPC endpoints for your production traffic, then you are currently in a structural vulnerability from which code optimizations will not save you. The risks associated with this are well known, but let’s go over what could go wrong if you are not familiar with them.
Rate Limiting at the Worst Moments
- Shared Solana RPC API endpoints have a set of rate limits that apply to all users, and these rate limits do not account for your application’s individual needs.
- When network congestion occurs, such as during NFT mints, token launches, or even macro-economic events, shared Solana RPC endpoints can be a bottleneck exactly when you need them most.
- Rate limiting on a DEX or trading protocol during high volatility translates directly to lost revenue and user churn.
- There is no escalation path on a public endpoint. When you hit the limit, you wait.
Data Integrity and Staleness
- Shared Solana RPC nodes often operate under resource constraints that can cause them to serve slightly stale data, especially under load.
- Applications relying on real-time account data, such as wallets, trading interfaces, liquidation bots, can make decisions based on outdated state.
- A Solana RPC node that is only one or two slots behind can cause simulations of transactions to fail or produce erroneous results.
- Audit trails and compliance reports can become complicated when your infrastructure is not capable of guaranteeing the timeliness of the information being served.
Security and Privacy Vulnerabilities
- Shared RPC endpoints mean your transaction data flows through infrastructure you do not control, alongside traffic from unknown third parties.
- Request patterns visible at the RPC layer can leak information about your trading strategy, liquidation thresholds, or wallet behavior.
- Public Solana RPC API access points are often the target of monitoring for MEV bots seeking to front-run or sandwich a transaction.
- You have zero capability to implement controls, IP whitelisting, or even authenticate requests without your own infrastructure.
No SLA, No Accountability
- Public and shared providers carry no service level agreement. Downtime is absorbed entirely by you.
- Support response times for free or shared plans usually involve days, not minutes, which is not suitable for production use cases.
- In many cases, you won’t even be aware if your Solana RPC node is experiencing degradation until users complain.
- There is no recourse or way to recover losses without contractual accountability.
Don't let a shared Solana RPC node become your next incident. Upgrade your Web3 infrastructure with dedicated nodes.
How Dedicated Solana RPC Infrastructure Reduces Operational Risk
The move from shared to dedicated Solana RPC infrastructure is not simply a performance upgrade, it is a fundamental shift in how you manage counterparty exposure. When you own or lease dedicated nodes, you change the risk profile of your entire operation.
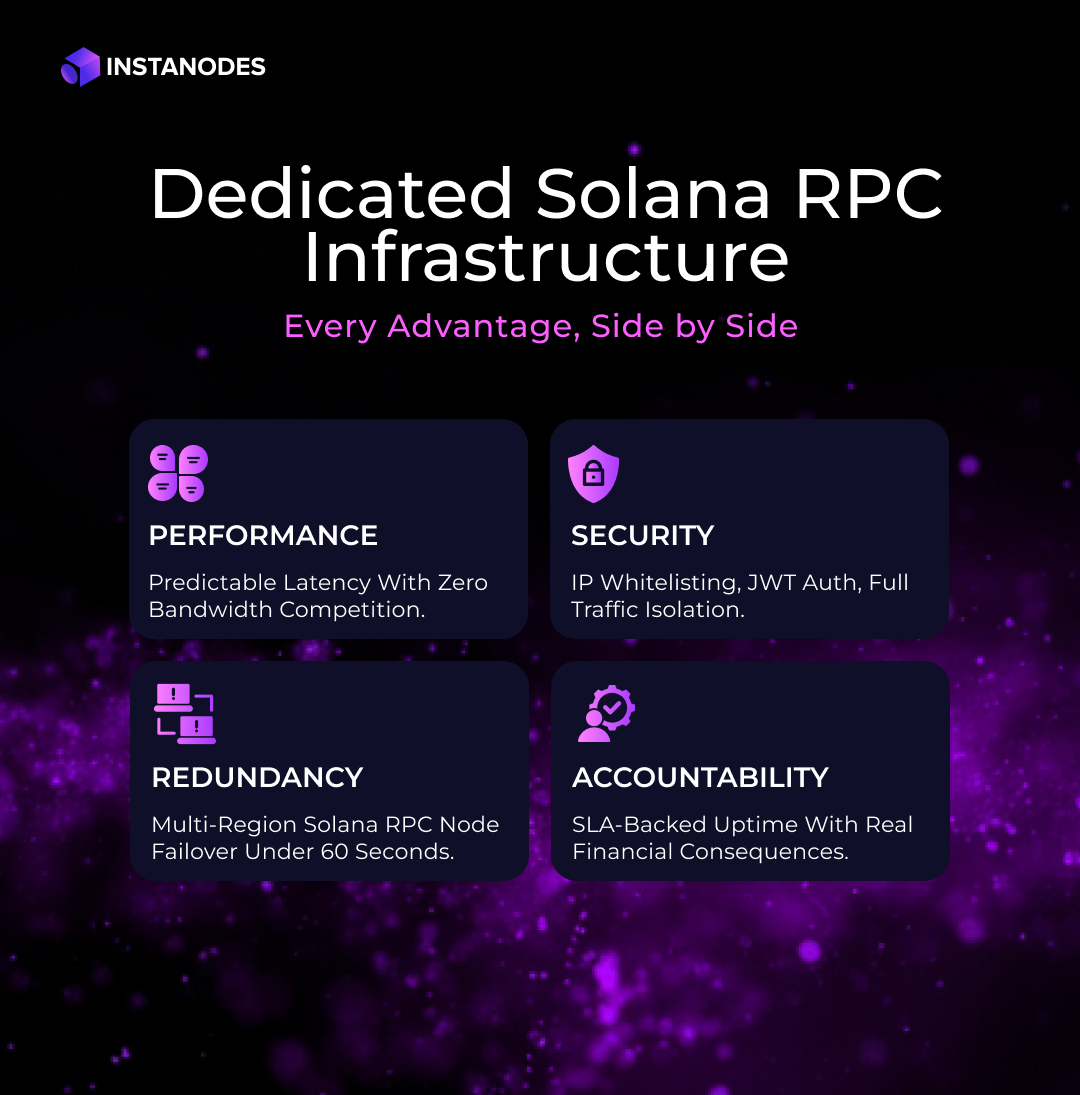
Isolation Eliminates Noisy Neighbor Risk
- Dedicated Solana RPC nodes serve only your traffic. There is no competition for bandwidth, memory, or processing capacity with other teams.
- This isolation means your performance is predictable. You can model capacity, design for peak demand, and create relevant latency SLAs.
- The noisy neighbor effect, in which increased usage by one user hurts all other users, is eliminated in the architecture.
- Teams operating dedicated infrastructure report significantly higher transaction success rates during Solana network congestion events.
Custom Configuration and Optimization
- With a dedicated Solana RPC node, you can adjust configuration settings according to your specific application need, which may be high-frequency trading, NFT minting, or indexing.
- With custom RPC calls, better websocket settings, and archival data access, dedicated plans can be configured in ways that shared plans cannot.
- Node versioning is in your control. You can coordinate upgrades with your deployment cycle rather than absorbing unannounced changes from a shared provider.
- Dedicated setups allow for geographic co-location, reducing the physical latency between your computer and your Solana RPC API endpoint.
Redundancy and Failover Architecture
Some good practices the best Solana RPC provider include:
- Multi-region node deployment with auto-failover to prevent a data center issue from bringing your product down.
- Using a cluster of load balanced Solana RPC nodes to provide availability even when a node is down due to maintenance.
- Using active monitoring to provide sub-minute failover times to minimize the mean time to recovery for your product.
- Redundant infrastructure transforms counterparty exposure from a binary risk into a managed, distributed one.
Security Controls You Actually Control
- Dedicated Solana RPC infrastructure allows you to implement IP whitelisting, JWT authentication, and rate limiting tuned to your own risk tolerance.
- Traffic isolation ensures that your own transaction patterns are not observable with the patterns of others using the endpoint.
- Implementing your own DDoS mitigation solution provides a defense in depth that endpoints cannot provide in a shared state.
- Dedicated nodes make compliance much simpler for us, as we can identify exactly where the data is being processed, by whom, and under what terms and conditions, which is particularly important for teams that are under regulatory pressure.
The Provider Relationship Itself Matters
- The best Solana RPC provider is not just a technical vendor, it is an operational partner. Dedicated arrangements typically include direct access to technical support, proactive monitoring, and escalation paths that shared plans exclude.
- The financial accountability of the SLA-backed uptimes guarantees shifts some of the operational risk back onto the service provider.
- The transparent pricing of the dedicated infrastructure eliminates the cost variability of the usage-based shared plans during traffic events.
- A true infrastructure partner will notify you of changes in the Solana network, validator issues, and RPC changes before they affect your end-users.
Concluding Thoughts
Counterparty exposure in Solana RPC infrastructure is a slow-burn risk, which remains invisible during normal operations and catastrophic during the events that matter most. Those who discover their dependency on shared endpoints during an outage pay a price far exceeding the cost of dedicated infrastructure.
The transition to a dedicated Solana RPC node is not just about faster speed or higher throughput. It is about owning your operational risk, building resilience into your product’s foundation, and making a commitment to reliability that your users can feel. You might be running a DeFi protocol, a wallet, a DEX aggregator, or a trading platform; the Solana RPC node beneath your application is a business-critical asset.
At Instanodes, we build dedicated Solana RPC infrastructure for those who cannot afford to treat their blockchain connectivity as an afterthought.
Ready to eliminate counterparty risk from your Solana stack? Talk to us today!